I may be dating myself with the Naughty by Nature OPP reference, but I couldn’t get it out of my head. The Internet of Things (IoT) is the next big thing in the high-tech industry and with consumer products. At its core, the IoT is devices that weren’t previously internet connected, but now are. They are “smart” products: your new thermostat, your new fridge, your new garage door opener, security cameras, and so on. I was a bit slow to adopt any of these because of security concerns I had.
If those devices can get out to the wilds of the internet, then perhaps things can get in too. The most famous incident with IoT devices so far is when devices infected with the Mirai malware were made to perform a DDOS attack on DNS provider Dyn last October. They brought down or affected small services you may have heard of before like Netflix, Amazon.com, Yammer, AirBnB, and many more. This is an artist’s interpretation of the Mirai botnet:
Recently I decided to walk down the road of IoT adoption partly as an experiment, partly to become familiar with new technology, and mostly because it’s a lot of fun to just say, “Alexa, turn on the outside lights”, “Alexa, what’s the weather?”, or “Alexa, set the house to 68 degrees” without having to take out my phone or, better-yet, get up. My adoption of the IoT started with a single Amazon Echo Dot and quickly extended into more Echo Dots for whole-house coverage, most of my house lighting through ZigBee-enabled lights, a Wink Hub2 to act as a bridge between the lights and my Dots, a Nest thermostat, and Nest Protects.
My security concerns were still there though, and a botnet was really the least of my concerns. I am more concerned with the compromising of one of these devices to be used as a proxy to attack my home network and capture sensitive information. I decided to do a home network audit and snoop on these devices to see exactly what they were doing.
I started by writing down every internet-connected device in my home: iPhone’s, iPad’s, cable boxes, computers, etc. I then used a network information gathering tool called Zenmap to scan my network for devices, their OS, and their open ports. I compared the two to see if there was anything missing or perhaps an intruder there.

…a botnet was really the least of my concerns. I am more concerned with the compromising of one of these devices to be used as a proxy to attack my home network and capture sensitive information.
After everything checked out there, I wanted to sniff all the traffic occurring on my network. I did this by using the Man In The Middle Framework to ARP poison my networking forcing all traffic to be routed through my computer.
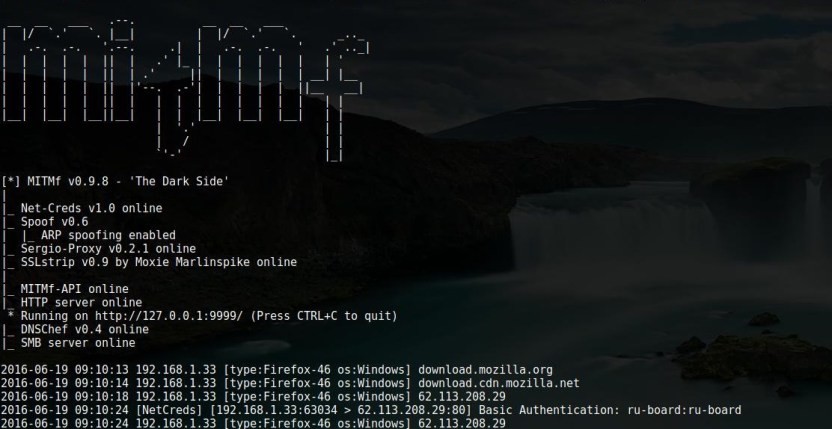
I also used two programs for session hijacking that would show me cookies being passed. I did this because malicious activity may not always be obvious just from request destination and origination. The two programs are called Ferret and Hamster.
All my new IoT devices checked out fine. True it was a small glimpse into their overall activity, but I was happy to see nothing crazy was going on. However, an old device looks like it was infected. I use a Gen1 Amazon FireTV Stick. I can’t completely blame the stick itself. I had opened it up to unsigned apps in order to run an app that will remain nameless to stream TV and movie content. Every 4 hours, I saw it do an HTTPS form submission. From appearances, it was simply pinging a website in China telling it that it was alive, what language it uses, and what its operating system is. Yes, my TV is in a botnet. I didn’t pick up any other suspicious activity from it since except for the regular pings.
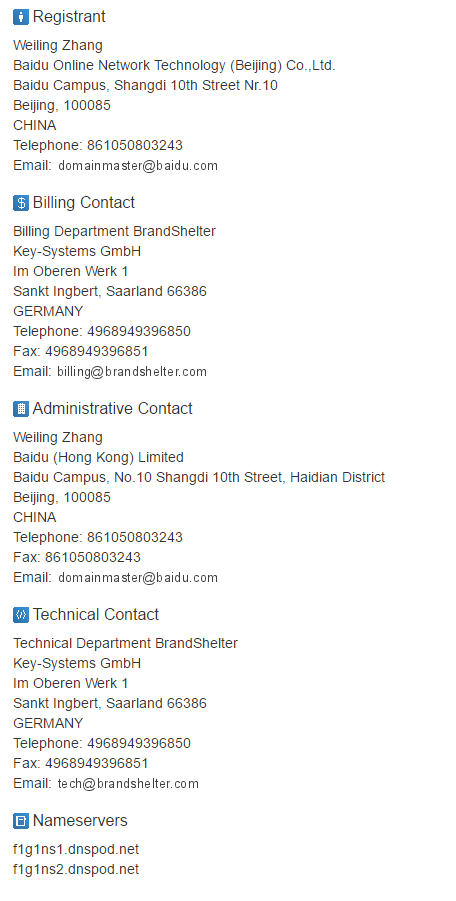
The website it’s going to (nrc.tapas.net) is registered to Baidu Technology, which is like the Google of China. Here are the registration details:
Yes, my TV is in a botnet…
I have contemplated sending an email asking them what gives. Key-Systems is a registrar, and I’m unsure if Baidu does webserver/webservice hosting that may make registration information look like this. Either way this doesn’t seem like legitimate activity for an Amazon device with only one non-standard app installed on it. I have a couple Amazon Fire Tablets with this same app and neither of them exhibited this behavior. It may just have been bad luck. I’ve ordered a Gen2 FireStick from Amazon as a replacement. I’m curious if it will do the same thing.
Beware the IoT. I’m pretty safe and knowledgeable, and my household was still hit. With that said, it was only a single device and one I had essentially rooted. I’d imagine that without the hacking, it would be far less vulnerable. Still, it’s something to keep in mind as you adopt this technology for your own home.



